What is a Zero Trust approach to cybersecurity?
Zero Trust is a proactive, integrated approach to security across all layers of the digital estate that explicitly and continuously verifies every transaction, asserts least privilege, and relies on intelligence, advanced detection, and real-time response to threats.
What are the Benefits of Implementing this approach?
- Improve user experience and productivity because it empowers people to work productively and securely when, where, and how they want.
- Apply to your entire digital estate – prioritize milestones based on the most important assets first.
- Integrating verification and controls across security pillars allows you to unify your strategy and security policy.
- Monitor your security posture with strong governance includes validating business assertions assessing security posture and understanding the impact of security culture.
- Automate to simplify and strengthen your security posture, reducing manual efforts so security teams can focus on critical threats.
Where are you at in the Maturity Model?
First Stage
- Are you using Multi-factor Authentication for passwords and providing Single Sign On access to cloud apps?
- Do you have visibility into device compliance, cloud environments, and logins to detect anomalous activity?
- Are your networks segmented to prevent unlimited unilateral movement inside the firewall perimeter?
Significant Progress
- Are you using real-time risk analytics to assess user behavior and device health to make smarter decisions?
- Can you correlate security signals across multiple pillars to detect advanced threats and quickly take action?
- Are you proactively finding and fixing vulnerabilities from misconfigurations and missing patches to reduce threat vectors?
Most mature stage
- Are you able to dynamically enforce policies after access has been granted to protect against violations?
- Is your environment protected using automated threat detection and response across security pillars to react more quickly to advanced threats?
- Are you analyzing productivity and security signals to help drive user experience optimization through self-healing and actionable insights?
Don’t despair if you are still in the First Stage
Research has shown that Multi-factor authentication reduces the effectiveness of identity attacks by more than 99%. Taking just this one/first step in the First Stage can offer big rewards. If you use Active Directory for your office computers, you should consider enabling MFA or other secure methods of sign-in to computers such as Visual Facial Recognition. For your Office 365 installation, you should enable multi-factor authentication. Once your admin has done that, this is a nice article https://support.microsoft.com/en-us/office/set-up-your-microsoft-365-sign-in-for-multi-factor-authentication-ace1d096-61e5-449b-a875-58eb3d74de14#:~:text=1%20Check%20whether%20your%20Office%20365%20%22admin%20has,watch%20the%20video%20to%20learn%20more.%20See%20More highlighting the steps each user needs to take to set up their own account to use it. After admin level setup, the first time the user logs into to office online, they will be prompted to setup any missing needed information. If your users typically do not use office online, the setup provides you with a link you can send them to, to setup this information.
Zero Trust is an ongoing journey. Getting started begins with simple first steps, a continuing urgency, and continuous iterative improvements. Get started today!
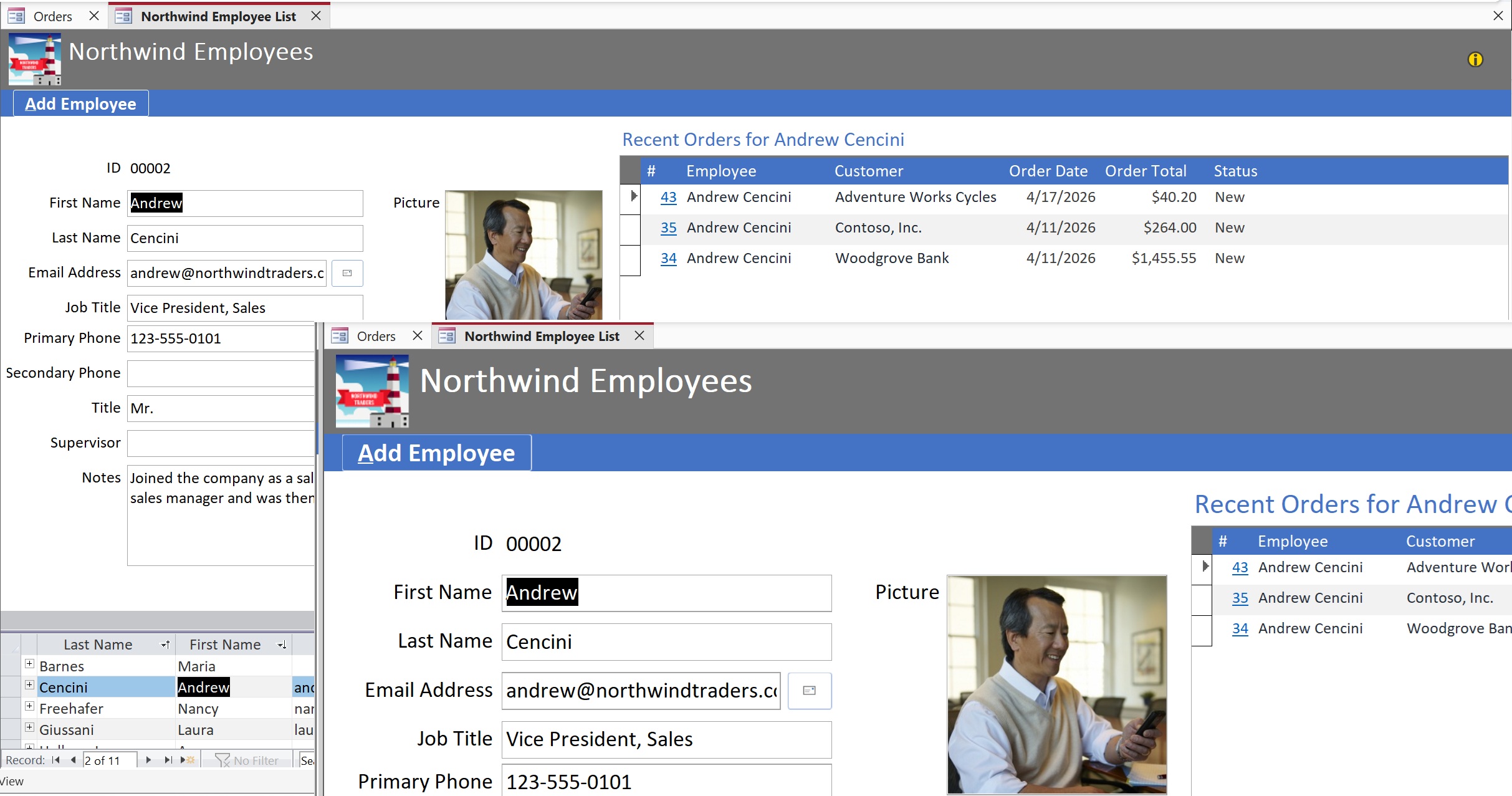
What types of recommendations does Microsoft have for securely using Microsoft 365?
Microsoft now recommends that you set the Macro Settings in the Trust Center in Microsoft Access and Excel to “Disable all macros except digitally signed macros”. If you do this, there are then two ways to run a Microsoft Access application with VBA Code or an Excel workbook with Macros. The first is to sign the code. Barnes Business Solutions can help you do this. Contact us at mbarnes@BarnesBusinessSolutions.com if you would like an application developed by us, signed. See https://support.microsoft.com/en-us/office/show-trust-by-adding-a-digital-signature-5f4ebff3-360d-4b61-b2f8-ce0dfb53adf6 for more details on this digital signing process in Microsoft Access. This is currently rolling out for Office 365 users. Note that you need an enabled version to sign the code. Any office version can use digitally signed code.
For those of you who are Access VBA developers, there are also a couple of good sources for how to do digital signing on your own. See this recorded Access Lunchtime webinar https://youtu.be/D2QNkOaxanA where I demonstrate the signing process and provide further information on it. In the video description, if you hit “Show more” you will also find a link to the PowerPoint and a link to a great article by Colin Riddington that also provides how to information with a slightly different take/viewpoint. Both are well worth your time.
See https://www.cisecurity.org/benchmark/microsoft_office for Microsoft’s complete recommendations on securely using Microsoft 365. Page 75 is the one that suggests to Ensure ‘VBA Macro Notification Settings’ is set to ‘Enabled: Disable all Except Digitally Signed Macros’.
The second way to run applications with the “Disable all macros except digitally signed macros” setting set, is to add your code location as a Trusted location. However, many companies are turning off the ability for users to do this, so signing your application may be a better approach. There are recommendations in the CISSecurity guide, page 64 to disable Trusted Locations on the Network. And on page 66 to disable all Trusted Locations added by the user.
What’s next for Zero Trust?
In the upcoming months, Microsoft expects to accelerate the unification of policies across pillars to simplify unified policy enforcement. They are helping to provide automated threat intelligence to empower security teams to correlate signals across pillars and prioritize threats. There are plans to implement Zero Trust principles in software and DevOps processes to help implement a Zero Trust approach without needing to retrofit applications. Security posture management will increase the efficiency of configuring and managing policies by assessing risks like configuration drift, missed software patches, and gaps in security policies.
Don’t delay on getting started making your environment more secure! Contact us or book your free half hour consultation today!